RESEARCH
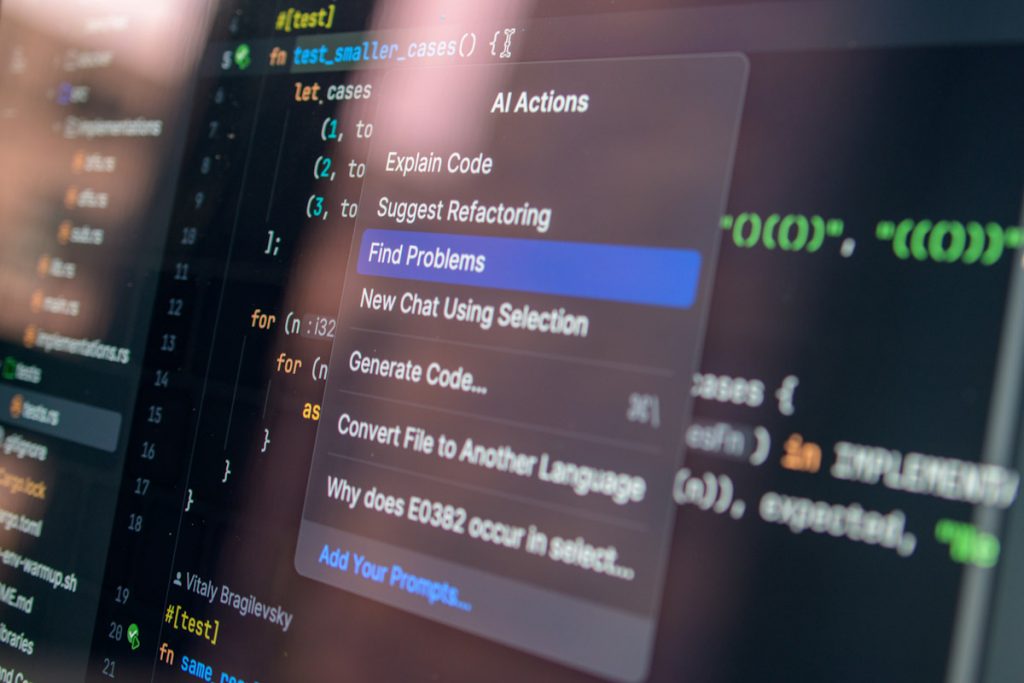
Your AI Agent Visits Websites on Your Behalf. Attackers Are Leaving It Notes.
The last two years of AI adoption inside businesses have followed a pretty consistent pattern. A team tries a tool, it saves them time, word gets around, and suddenly half the company is using something IT didn't approve. Now those ...
Cyber Compliance
Stop Getting Mad When Your Client Won’t Buy Compliance

You know the look. You explain how they need MFA, a risk assessment, documented policies, backups that actually restore… and your client stares back at you like you just recited the GDPR in ancient Greek. You leave the meeting frustrated. ...
“Fined Without a Breach?” Why the Wojeski $60,000 Penalty Matters—even if You Think You’re Small

You’ve seen two kinds of headlines after cyber incidents: (1) lawsuits and (2) regulatory enforcement. The recent $60,000 fine against Wojeski ...
New California Audit Law Just Put Your MSP on the Hook. Here’s How to Turn It Into Recurring Revenue

If your clients process sensitive data, your MSP is now part of the legal conversation. On July 24, 2025, California finalized new rules that require businesses processing high-risk personal information to undergo annual, independent cybersecurity audits. This isn’t just for ...
Cyber Liability
One Misconfigured AI Agent Can Impact Every Client You Manage

When One Action Hits Every Client, Governance Decides the Outcome Imagine a hypothetical that’s taught in law school every semester: A delivery driver abandons his route to join a drum circle for three days. On his way back, he causes ...
They Already Have an IT Department. Good. That’s Why You Should Call.

Last night I was at dinner with the CEO of an MSP. Good operator. Growing. Adding clients. Doing the work. We were walking around his town before dinner talking about the usual founder stuff. Processes. How to get people to ...
Agentic AI at the Edge: Opportunity, Autonomy & the Coming Legal Minefield

You’ve probably heard executives gush about autonomous AI agents, the shiny new productivity booster that can automate workflows faster than you can say “zero-trust.” But what they don’t hype is how agentic AI turns your cybersecurity playbook into an existential ...
Insurance & MSP Liability
The Clients You're Ignoring Are the Ones Who Will Sue You

I said something on stage at XChange last week that made a lot of people in the room uncomfortable. "Your smallest clients are your biggest risk." Not your enterprise accounts. Not the ones with complex environments and demanding SLAs. The ...
You’re Not Insured. You’re Just Hopeful.

So there I am, wrapping up a conference session—over 1,000 MSPs in the building—and one guy comes up clutching a fresh copy of Standardized like it’s a fire extinguisher in a server room. He’s nodding along, clearly rattled in all ...
Your MSP Carries More Risk Than a Magazine Stand—and That’s a Problem

Let’s talk about airport gift shops for a minute. You know the ones—tiny kiosks with $14 neck pillows, expired jerky, and three copies of Men’s Health no one’s ever going to read. Now, tell me—how much sensitive data do you ...
More Articles
Your OSINT Reality Check: Here’s What an Attacker Is Finding in 30 Minutes or Less
Today’s connected, AI-driven digital ecosystem has made it easier than ever to build a professional brand, network with peers, and share ideas with a wider audience. It’s opened doors for businesses that simply didn't exist before: new customers, new partnerships, ...
Value That Converts: Why Your vCSO Pitch Keeps Getting Pushed to IT
You walked out of that meeting feeling like a closer. Your credentials were on point. You covered the whole stack: EDR, SIEM, MDR, quarterly risk assessments, tabletop exercises, NIST alignment. Your vCSO offering was solid. You even had a phased ...
Part 2: Threat Actors Don't Pick You. You Just Happen to Be There.
In Part 1, we established that Handala didn't pick Stryker off a strategic target list and then figure out how to break in. They found access, recognized the value, and used it. That's still a deliberate, damaging attack—it just means ...
Part 1: Threat Actors Don't Pick You. You Just Happen to Be There.
There's this idea that floats around—usually in boardrooms and in forums—that advanced threat actors operate like surgeons. They pick a target, they plan it out, they execute. Super deliberate. Undeniably cinematic. It implies that a breach is something that happens ...
One Misconfigured AI Agent Can Impact Every Client You Manage
When One Action Hits Every Client, Governance Decides the Outcome Imagine a hypothetical that’s taught in law school every semester: A delivery driver abandons his route to join a drum circle for three days. On his way back, he causes ...
The Clients You're Ignoring Are the Ones Who Will Sue You
I said something on stage at XChange last week that made a lot of people in the room uncomfortable. "Your smallest clients are your biggest risk." Not your enterprise accounts. Not the ones with complex environments and demanding SLAs. The ...
Part 2: Incident Response: Panic Is Not a Phase, It’s a Symptom
Turning Incidents Into Improvement Instead of Repetition When an incident finally ends, most organizations do the same thing: they exhale. Systems are back online. Alerts stop firing. Customers stop calling. Leadership announces that things are “under control.” Usually right before ...
Part 1: Incident Response: Panic is Not a Phase, It's a Symptom
Why Incident Response Fails Before the Incident Starts Most organizations think they’re “doing incident response” because they bought a tool. Or three. Maybe they even survived an incident once or twice, so clearly they’re fine now. That’s not incident response. ...
They Already Have an IT Department. Good. That’s Why You Should Call.
Last night I was at dinner with the CEO of an MSP. Good operator. Growing. Adding clients. Doing the work. We were walking around his town before dinner talking about the usual founder stuff. Processes. How to get people to ...
Agentic AI at the Edge: Opportunity, Autonomy & the Coming Legal Minefield
You’ve probably heard executives gush about autonomous AI agents, the shiny new productivity booster that can automate workflows faster than you can say “zero-trust.” But what they don’t hype is how agentic AI turns your cybersecurity playbook into an existential ...
Notepad++ Compromise: What you need to know
The recent Notepad++ compromise should make you pause for a moment because the Chrysalis backdoor is exactly the type of malware ...
Your Best Salespeople Aren’t in Sales. They’re on the Floor.
Last night I went out to dinner. I’m an early-to-bed guy, which means I eat when restaurants are still serving happy hour menus. This was New Orleans, so happy hour still meant good food and strong opinions. I was halfway through an appetizer when I overheard ...


